IEC 60880
IEC 60880:2006 (Nuclear Power Plants – Instrumentation and Control Systems Important to Safety – Software Aspects for Computer-Based Systems) is a functional safety standard which, together with IEC 62138, covers the software aspects of computer based systems used in nuclear power plants to perform functions important to safety. IEC 60880 provides requirements for the safety category A as defined by IEC 61226.
Fitness for purpose litigation against companies and individuals is now an increasing risk. IEC 60880:2006 is a technical standard used by lawyers to interpret laws. The relevant law in question for Europe is the General Product Safety Directive 2001/95/EC (GPSD). This states that the product creator has the responsibility to develop a safety critical product in a way which is compliant with ‘State-of-the-Art’ development principles. ‘State-of-the-Art’ simply refers to commonly accepted best practices, which in the case of nuclear electronic safety related systems are now embodied in IEC 60880:2006. Where companies fail to employ accepted industry practices, they cannot use the “State-of-the-Art” legal defence against such litigation.
Recommended tools for compliance with IEC 60880
QA Systems enables organisations to accelerate IEC 60880 compliance with automated static analysis and software testing tools:
STATIC ANALYSIS
Tool Certification & Qualification
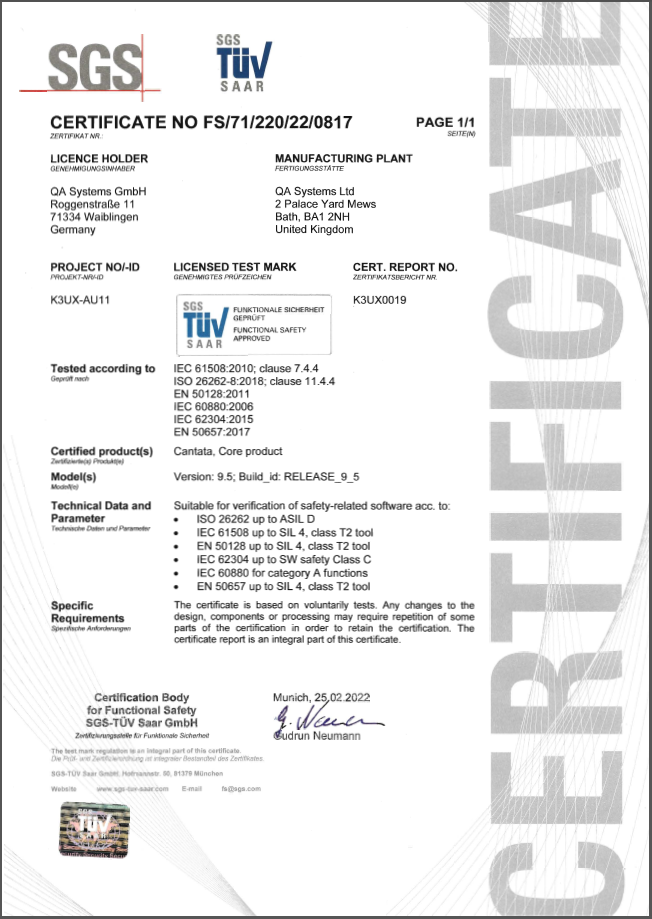
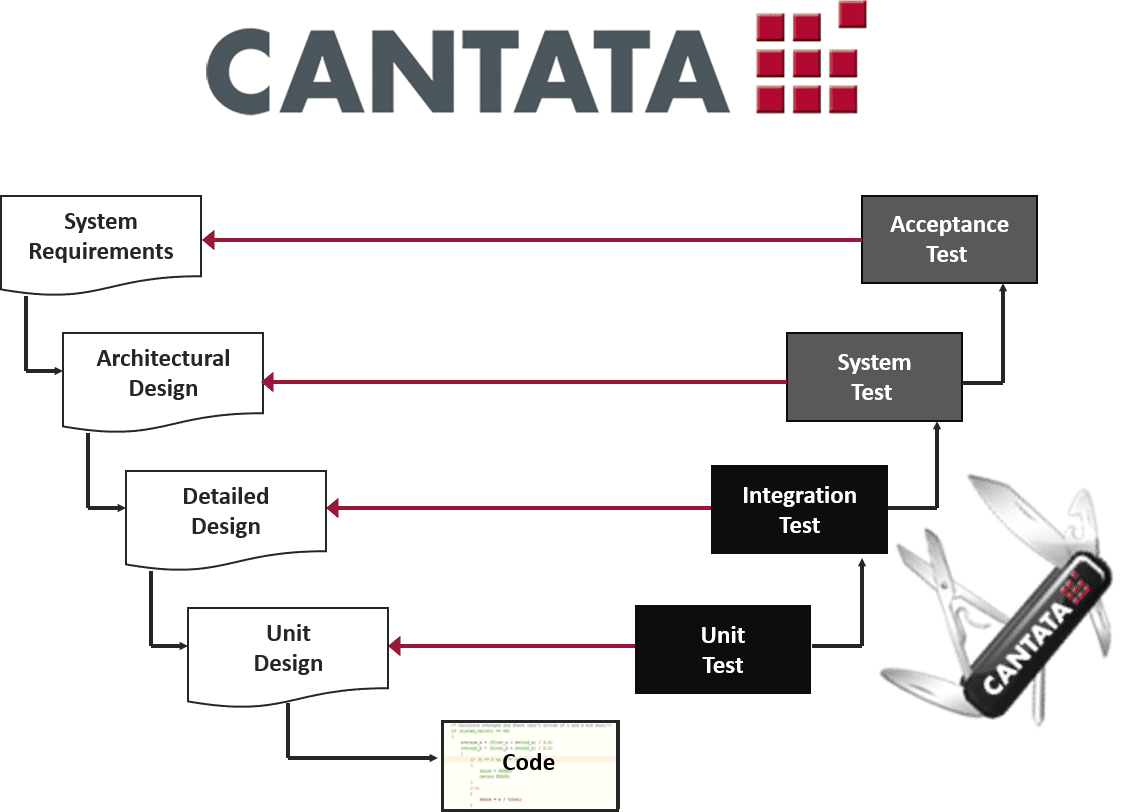
QA Systems’ tools have been classified and certified by SGS-TÜV GmbH, an independent third party certification body for functional safety, accredited by Deutsche Akkreditierungsstelle GmbH (DAkkS). Cantata has been certified as usable in development of safety related software according to IEC 60880:2006.
The tool certification kit for IEC 60880 is available to ease our customers’ path to certification. This contains everything needed to prove that Cantata fulfills IEC 60880 recommendations as well as guidance to help you to achieve compliance.
For our static analysis tool QA-MISRA, our tool Qualification Support Kit (QSK) automatically executes a full tool qualification verification test suite on the installed tool configuration and generates the necessary reports for IEC 60880 tool qualification.
These tool kits for IEC 60880 are available to ease our customers’ path to certification. They contain everything needed to prove that Cantata and QA-MISRA provide the required confidence in the use of software tools under IEC 60880 recommendations as well as comprehensive and detailed guidance on how to use them to comply with the required software verification activities of IEC 60880.
Please contact us for more information about these tool kits.
Software testing for IEC 60880 compliance
Cantata helps accelerate compliance with the standard’s software testing requirements by automating:
Please contact us for more information on Cantata for IEC 60880.
The IEC 60880 requirements for software testing and how these are supported by Cantata are summarised in our White Paper “Cantata Standard Briefing IEC 60880:2006”.
Start a free trial & get a complete copy of Cantata to evaluate using your code.